The Securities and Exchange Commission (SEC) recently released a proposed rule that would require public companies to implement new cybersecurity risk management and disclosure measures.¹ The proposed SEC cybersecurity disclosure rules aim to modernize and standardize the SEC’s approach to cybersecurity risk management by updating and expanding its guidance to companies regarding their disclosure obligations and internal controls over cybersecurity risk management.
The proposed rule would require public companies to assess their cybersecurity risk management programs and report to the SEC about their cybersecurity risks, incidents, and material impacts. The rule would also require companies to have internal controls over their cybersecurity risk management programs and to disclose any material weaknesses in those controls.
The proposed rule would also require companies to disclose the cybersecurity experience of their board of directors or nominees, or explain why they do not have any cybersecurity expertise on their board. This requirement aims to ensure that companies have the necessary cybersecurity expertise to oversee and manage their cybersecurity risks effectively.
Cybersecurity Incident Disclosure Practices
The staff in the Division of Corporation Finance has noted that the disclosure of material cybersecurity incidents and risk management practices by registrants is inconsistent, may not be timely, and can be difficult to locate. The proposed rule amendments would enhance incident reporting to provide investors with more detailed information on material cybersecurity incidents, risk management practices, and board expertise in this field.
Proposed Cybersecurity Incident Disclosure Requirements
The proposed rules would require current and periodic reporting of material cybersecurity incidents, as well as periodic disclosures about a registrant’s policies and procedures for managing such risks. Additionally, these rules would require disclosure of the impact of cybersecurity risks on a registrant’s business strategy, management’s role in implementing their cybersecurity policies, and the board of directors’ oversight role and expertise in this area. These requirements are intended to help investors better understand cybersecurity risks and incidents related to companies so that they can make more informed investment decisions.
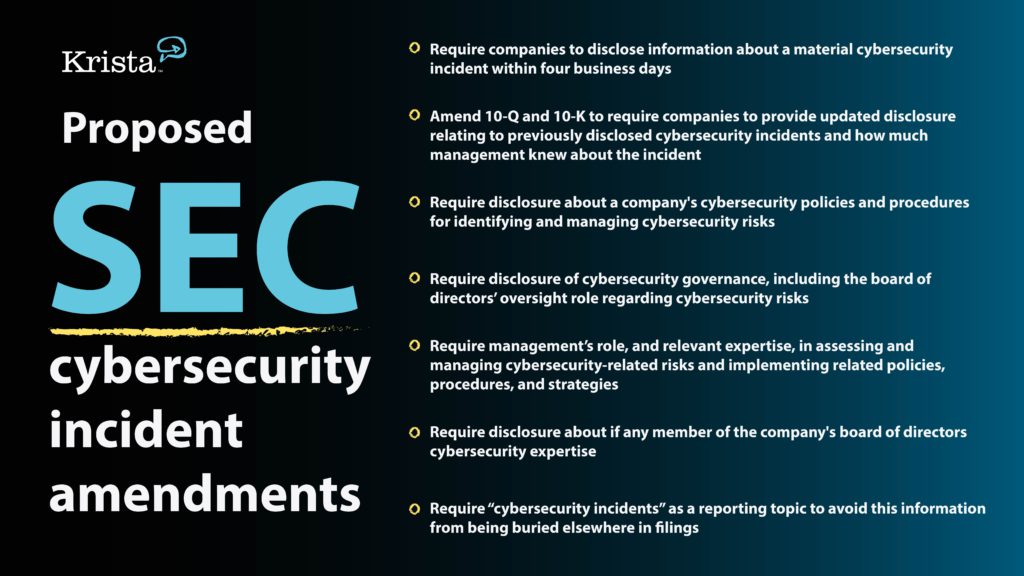
The proposed amendments include
- Amend Form 8-K requiring registrants to disclose information about a material cybersecurity incident within four business days
- Amend Forms 10-Q and 10-K to require registrants to provide updated disclosure relating to previously disclosed cybersecurity incidents and how much management knew about the incident
- Amend Form 10-K to require disclosure about a company’s cybersecurity policies and procedures for identifying and managing cybersecurity risks
- Amend Form 10-K to require disclosure of cybersecurity governance, including the board of directors’ oversight role regarding cybersecurity risks
- Amend Form 10-K to require management’s role, and relevant expertise, in assessing and managing cybersecurity-related risks and implementing related policies, procedures, and strategies
- Require disclosure about if any member of the company’s board of directors cybersecurity expertise
- Require “cybersecurity incidents” as a reporting topic to avoid this information from being buried elsewhere in filings
Why is the SEC proposing cybersecurity incident disclosure requirements?
The SEC’s proposed rule is intended to help investors understand the risks associated with investing in public companies. By requiring more detailed disclosure of cybersecurity incidents and risk management practices, investors can better assess a company’s security posture and make more informed decisions about whether or not to invest. Therefore the SEC is proposing to amend Form 8-K by adding new Item 1.05 requiring a company to disclose material cybersecurity incidents within 4 days:
- When the incident was discovered and whether it is ongoing
- A brief description of the nature and scope of cybersecurity incidents
- Whether any data was stolen, altered, accessed, or used for any other unauthorized purpose
- The effect of the incident on the registrant’s operations
- Whether the registrant has remediated or is currently remediating the incident
This information will help investors understand the severity of the incident and how it is being addressed.
Companies will need to disclose cybersecurity risk management, strategy, and governance procedures
Companies are increasingly exposed to cyber risks that can have serious financial impacts. For example, a company may suffer reputational damage, or face regulatory fines or legal judgments as a result of a cybersecurity incident. To help investors understand potential risks and the potential financial impact of these events, the SEC proposes requiring companies to disclose information about their cybersecurity risk management strategy, and how the board of directors is involved and oversees these procedures for identifying and managing cybersecurity risks, including operational risk; intellectual property theft; fraud; extortion; harm to employees or customers; violation of privacy laws and other litigation and legal risks; and reputational risk.
Specifically, proposed Item 106(b) would require disclosure about whether the company has conducted a cybersecurity risk assessment program, engages third parties in connection with this program, has policies and procedures for overseeing third-party service providers, takes steps to prevent, detect, and minimize the effects of cybersecurity incidents, has business continuity plans in case of an incident, has made changes in response to previous incidents, considers cybersecurity risks when making business decisions or allocating capital.
The goal is to provide financial stakeholders with greater transparency into how companies manage cybersecurity risks and operationalize cybersecurity policies so that they can make informed decisions about their investments. By requiring disclosure of this information as part of SEC filing requirements, investors will be able to better understand how a company is managing cyber risks and what potential impacts these risks might have on its results or financial condition going forward. In this way, companies and the board of directors are held accountable for taking appropriate action to protect themselves and their financial stakeholders from cyber risks.
How companies can use AI and automation to prepare for the proposed SEC cybersecurity rules
The SEC rules are going to impact the information security, risk, and IT departments in every public company…and likely every company that has public companies as their customers. In other words – almost everybody. If you report to the SEC, obviously this is now a government mandate and you will have to comply. Public companies will most likely rework their contracts with vendors to ensure they can comply in that four-day timeframe, so they stay compliant. If you are a private company and want to keep your public company customers as customers, you will voluntarily adopt the same levels of governance and reporting efficiency to support your public customers. The account executives that manage the relationships with public companies might say you were “voluntold” to comply.
Most public companies today likely use one or more GRC platforms such as Archer, MetricStream, NAVEX IRM (Lockpath), or ServiceNow. Many fit in the GRC category. Many companies still use a compilation of tools to manage their governance, third parties, cybersecurity, incidents, and reporting such as Excel, Jira, SharePoint and Outlook. The level of maturity of these programs varies across both public and private enterprises. One thing all the programs have in common no matter the tooling being used are the manual processes surrounding governance, risk, and compliance. Processes such as cybersecurity patching, third-party assessments, internal audits, incident reporting, business continuity efforts such as tabletop testing and plan execution, regulatory change management, compliance oversight, and more all have significant and timely manual processes associated with them.
The four-day response window required by the SEC will challenge and stress every incident management and reporting process. Third parties involved in cyber incidents will have far less than four days to report their findings to keep their customers compliant.
No matter your level of incident response and reporting maturity, AI and automation will be needed to improve the productivity and accuracy required to comply. The most basic steps companies should take today to improve their response time include:
- Document your cyber incident response processes. Be sure to include all your cyber processes including (but not limited to):
- Cybersecurity breaches
- Loss of hardware (such as laptop stolen)
- Third party loss of data
- Denial of service attack
- Ransomware
- Identify all the systems and people you interact with during the response and recovery in each process
- Identify all the information needed from 1 and 2 above you will need in the required reporting and the steps to create and submit the support
- Develop an AI strategy to automate and orchestrate the entire incident discovery to the reporting process to fulfill cybersecurity disclosure requirements
- Manual strategies will include AI, ML, NLP, Document Understanding, iPaaS, and the deployment and maintenance of these models.
- AI Orchestration platforms like Krista allow you to configure all the above simply, without code, without manual deployment of AI models, and without future maintenance.
- Document your cyber incident response processes. Be sure to include all your cyber processes including (but not limited to):
Preparing for proposed Item 1.05 of form 8-K
The SEC’s proposals for new Item 1.05 of Form 8-K and proposed Item 106(b) of the same form provide investors with greater transparency into a company’s risk management practices so that they can make informed decisions about their investments. By requiring companies to disclose information on cyber risks, incidents, policies, procedures, and board oversight, financial stakeholders will be able to understand how companies are managing such risks and what potential impacts those risks may have going forward. AI and automation solutions can help organizations take an inventory of tools and controls, create flexible frameworks for procedures, establish governance controls accessible via generative AI features and interfaces, as well as implement AI-assisted decision-making to guide management compliance reporting. In this way, companies and the board of directors can be held accountable for taking appropriate action to protect themselves, their financial stakeholders, and the public from cyber risks.
Ultimately, these SEC proposals are intended to provide investors with greater transparency around cybersecurity risk management practices so they can make more informed investment decisions. With this increased transparency comes an additional responsibility for companies to ensure that they maintain robust cybersecurity controls and policies to protect their company’s financial health as well as that of their stakeholders. By taking proactive measures such as utilizing AI and automation solutions, companies will be better positioned to meet the applied standards set forth by the SEC. In addition, by sharing information related to their efforts in managing cyber risks through disclosure requirements, organizations will provide investors with the insight needed to make more informed decisions about their investments.
Sources: